The Complete Ethical Hacking Course: Kali Linux 2025 Edition
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 6h 37m | 3.78 GB
Created by TechBlazes Academy
.MP4, AVC, 1280x720, 30 fps | English, AAC, 2 Ch | 6h 37m | 3.78 GB
Created by TechBlazes Academy
Ethical Hacking with Kali Linux 2025 – Master Penetration Testing, Web Application Hacking, Wireless Attacks, and More
What you'll learn
- Master Kali Linux Fundamentals:
- Install, configure, and navigate Kali Linux like a pro.
- Understand Linux commands, desktop environments, and tools essential for ethical hacking.
- Perform Penetration Testing and Vulnerability Assessment:
- Plan and execute successful penetration tests using industry-standard methodologies.
- Identify and exploit vulnerabilities in networks, web applications, and wireless systems.
- Execute Advanced Ethical Hacking Techniques:
- Conduct man-in-the-middle attacks, DNS spoofing, and password cracking.
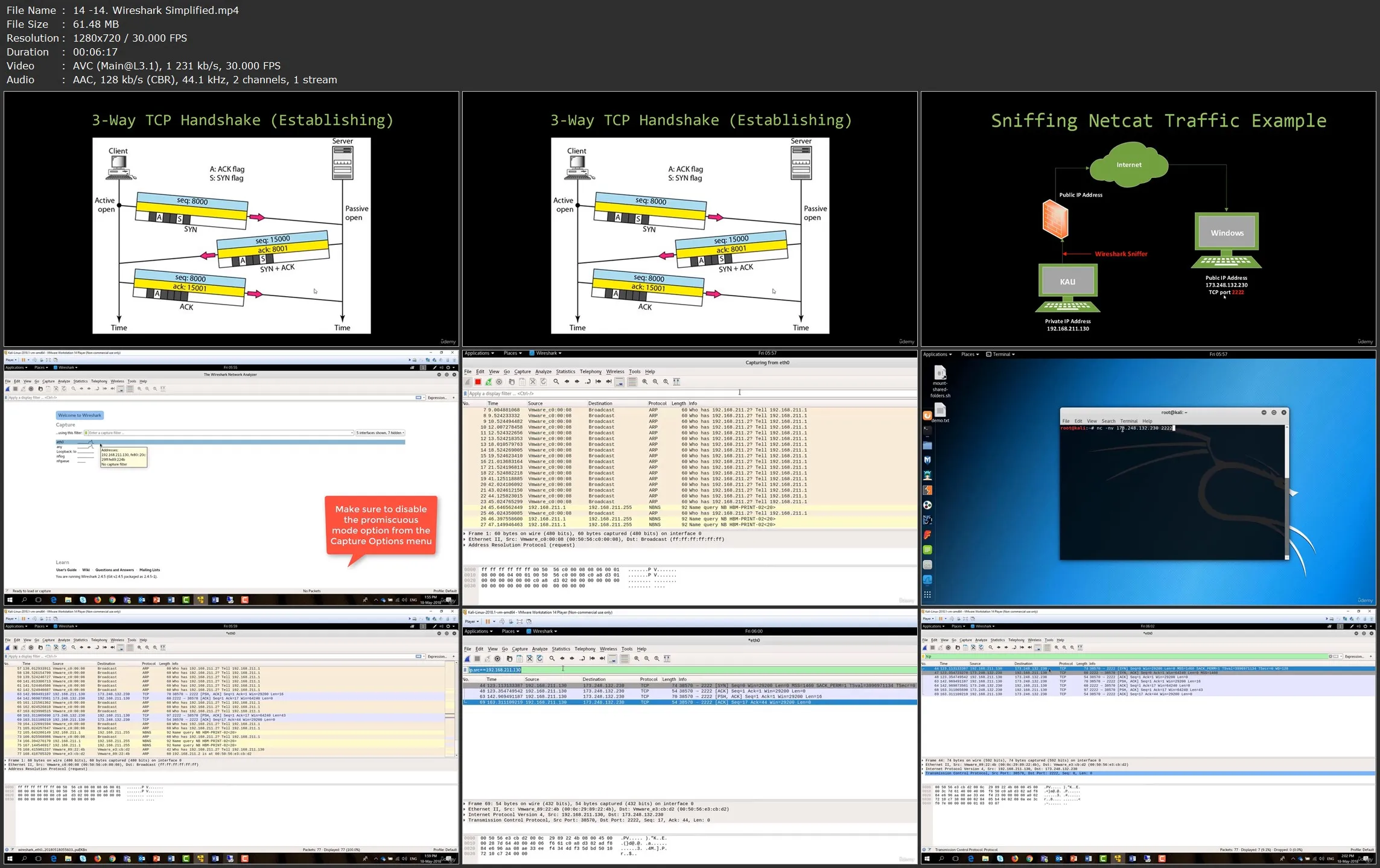
- Use tools like Metasploit, NMAP, Wireshark, SQLMap, and Armitage to exploit and secure systems.
- Secure Systems and Networks:
- Defend against common cyber threats like SQL injection, cross-site scripting (XSS), and ransomware.
- Implement best practices for network security, password management, and anonymity online.
- Explore Real-World Hacking Scenarios:
- Hack wireless networks (WEP, WPA, WPA2), WordPress sites, and Android devices.
- Create and deploy payloads, backdoors, and ransomware in controlled environments.
- Develop Professional Reporting Skills:
- Document and present penetration testing findings effectively.
- Learn how to communicate vulnerabilities and recommendations to stakeholders.
Requirements
- Basic Computer Skills
- A Computer with Minimum Specifications
- Virtualization Software (Optional but Recommended)
- A Willingness to Learn
- Stable Internet Connection
- Ethical Mindset
Description
Are you ready to step into the world of cybersecurity and become a skilled ethical hacker? Ethical Hacking with Kali Linux 2025 is your ultimate guide to mastering penetration testing, vulnerability assessment, and cybersecurity defense techniques using the most powerful tools available. Whether you're a beginner or an IT professional looking to advance your skills, this course will equip you with the knowledge and hands-on experience to protect systems, networks, and applications from malicious attacks.
In this comprehensive course, you’ll dive deep into Kali Linux, the industry-standard platform for ethical hacking, and learn how to use its tools to identify, exploit, and mitigate security vulnerabilities. From basic Linux commands to advanced penetration testing methodologies, you’ll gain the skills needed to secure systems and stay ahead of cybercriminals.
What You’ll Learn:
- Master Kali Linux: Learn how to install, configure, and navigate Kali Linux like a pro.
- Penetration Testing Fundamentals: Understand the steps to plan and execute successful penetration tests.
- Network Security: Perform port scanning, network reconnaissance, and man-in-the-middle attacks.
- Web Application Hacking: Discover vulnerabilities in websites, exploit SQL injections, and hack WordPress sites.
- Wireless Network Attacks: Crack WEP, WPA, and WPA2 encryption, and secure wireless networks.
- Password Attacks: Execute offline and online password attacks, design wordlists, and crack hashes.
- Social Engineering: Learn phishing techniques, OSINT (Open Source Intelligence), and Google Dorking.
- Mobile and IoT Hacking: Reverse engineer Android apps, hack IoT devices, and create a Wi-Fi jammer.
- Post-Exploitation Techniques: Install backdoors, create ransomware, and maintain access to compromised systems.
- Anonymity and Stealth: Stay anonymous online, bypass firewalls, and set up a command-and-control center.
- Reporting and Compliance: Learn how to document and present your findings professionally.
Course Highlights:
- 83 Hands-On Lectures: Step-by-step tutorials with real-world examples.
- Practical Labs: Apply your skills in simulated environments.
- Cutting-Edge Tools: Master tools like NMAP, Metasploit, Wireshark, SQLMap, Armitage, and more.
- Latest Techniques: Stay updated with the newest hacking methods and defenses for 2025.
- Beginner to Advanced: No prior experience required – we start from the basics and build up.
- Certification Prep: Gain the skills needed to pursue certifications like CEH (Certified Ethical Hacker) and OSCP (Offensive Security Certified Professional).
Who Is This Course For?
- Aspiring ethical hackers and cybersecurity professionals.
- IT professionals looking to transition into cybersecurity.
- Students and enthusiasts interested in learning penetration testing.
- System administrators and network engineers who want to secure their infrastructure.
- Anyone curious about how hackers operate and how to defend against them.
Course Requirements:
- A computer with at least 4GB RAM (8GB recommended).
- A willingness to learn and explore ethical hacking techniques.
- No prior experience with Kali Linux or hacking is required.
Don’t wait – the world of cybersecurity is evolving rapidly, and the demand for skilled ethical hackers is higher than ever. Whether you want to protect your own systems, start a career in cybersecurity, or simply satisfy your curiosity, this course will give you the tools and knowledge you need to succeed.